Is total security attainable for business owners in this increasingly digitalized world is the question on people’s mind following reports of hackers breaching one of the best video surveillance services company Verkada on Monday.
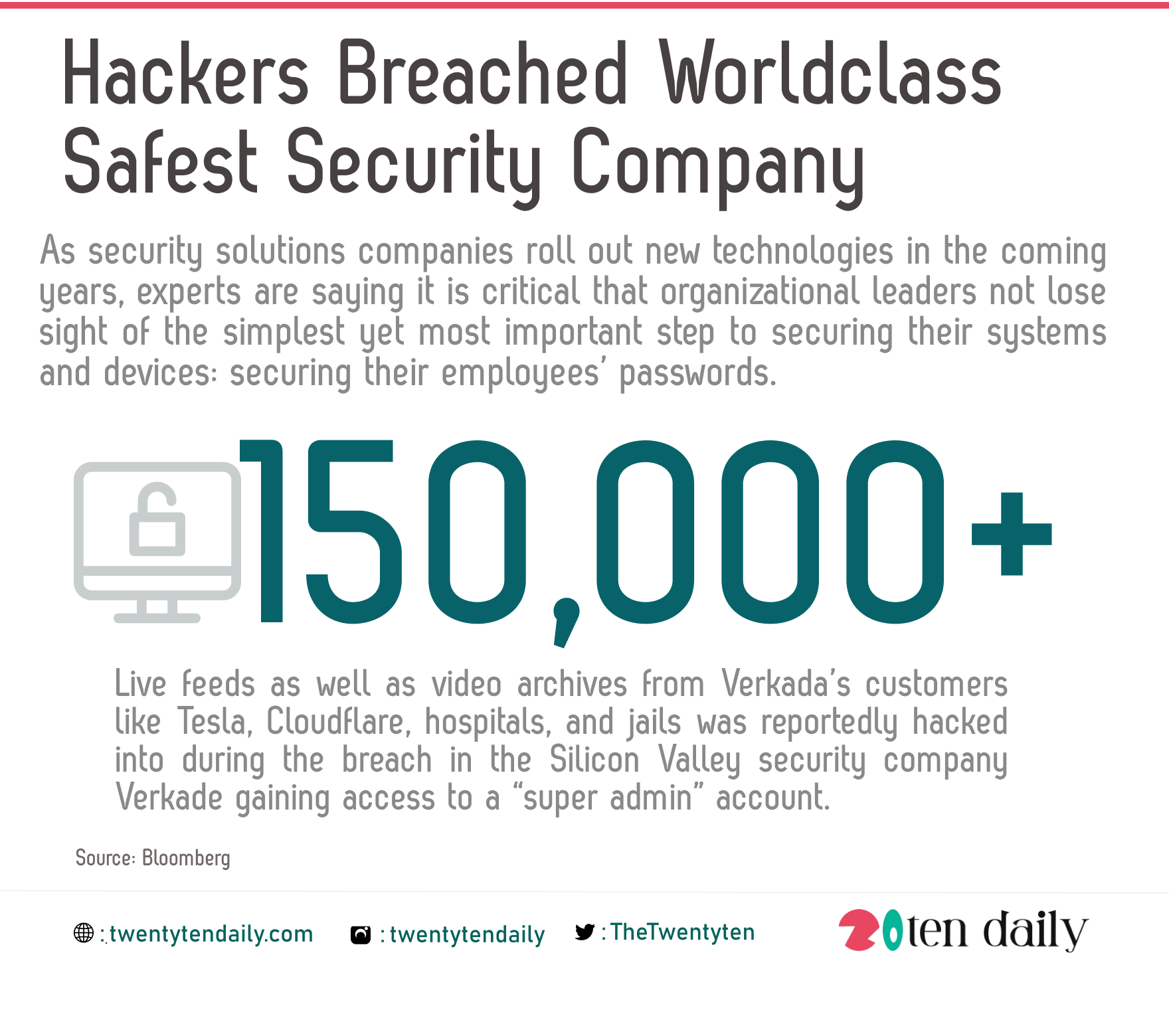
Bloomberg reported that Hackers breached Silicon Valley security company Verkade, gaining access to a “super admin” account that let them see more than 150,000 live feeds as well as video archives from Verkada’s customers like Tesla, Cloudflare, hospitals, and jails. Some cameras let the hackers access Verkade customers’ separate corporate networks.
Tillie Kottmann, one of the hackers who claimed credit for the breach, told Bloomberg the group’s goal was to expose how widespread surveillance has become and how easily it can be hijacked.
A Security Breach Through Compromised Password
According to Verizon, over 80% of successful cyberattacks are traced back to weak or compromised passwords. This would be the case for Verkade as not just any password was compromised but it’s “super admin” password that grants nearly unfettered access not only to all of Verkada’s surveillance cameras but also its most sensitive systems.
It gets worse. According to Dark Reading, this password was shared by over 100 internal users at Verkada.
Meaning a lot of people to grant “super admin” access to, particularly since the majority of organizations are adopting zero-trust security environments. Among other safeguards, zero-trust mandates that employees be given “least-privilege” systems access; this means that every employee is granted just enough systems access to perform their jobs, and no more.
Ultimately, it seems likely that the use of one super admin password available to over a 100 users could easily have been compromised.
What Could Have Been Done Differently
As security solutions companies roll out new technologies in the coming years, experts are saying it is critical that organizational leaders not lose sight of the simplest yet most important step to securing their systems and devices: securing their employees’ passwords. Here are some password security lessons from the Verkada breach:
- Require that all employees use strong, unique passwords for every work-related account and enable multi-factor authentication (2FA) on all accounts that support it.
- Implement role-based access control (RBAC) with least-privilege access. It’s difficult to conceive of a scenario where 100 employees would need “super admin” access.
- Deploy a business password manager company-wide and require employees to use it.

